I’m participating in Fun-a-Day 2014, a daily art challenge through the month of January, committed to do a daily post here detailing some Big Art Idea or project that looms somewhere out in my future.
After recently rereading Michel Foucault’s seminal and familiar essay “Panopticism” from Discipline and Punish which focuses on the centralization of power and surveillance, and reading Alexander Galloway and Eugene Thacker’s “Nodes” in The Exploit: A Theory of Networks focusing on the decentralization of power I had some thoughts about control in a networked context.
We assume there is an iron hand behind the back, an attempt to control us in conventional ways that comes with our access to networks and corresponding loss of privacy. What if there is no controlling hand, just control over the networked protocols we use and a corresponding profit in information about us?
While we are familiar with (and familiar with resisting) centralized control, we have an intuition that old modes of control become outdated and ineffective in a decentralized and networked society. To be sure, imprisoning and torturing the body are still effective means to reach an individual, but not necessarily effective at stopping an idea, a movement, or destroying networked resistance. When people are loosely affiliated, connected over networks, and united by ideas and larger goals, it is much more difficult to exert control in the old usual totalitarian ways.
Or to quote Fred Hampton of the Oakland Black Panthers assassinated by the FBI and Chicago Police in 1968:
You can jail a revolutionary, but you can’t jail the revolution.
Fred Hampton
Fred Hampton is saying that centralized authority can imprison, torture, and assassinate individuals, but with their old ways of centralized control cannot contain networked and decentralized movements. And he’s right, but we couldn’t expect authority to stay ignorant forever. In the early oughts, a systemic crisis prompted agents of the state and capital to adapt and seriously address networked resistance.
It was refreshing to read Brian Holmes’s 2007 essay The Revenge of the Concept: Artistic Exchanges, Networked Resistance , and strange to read something serious about the anti-globalization movement that didn’t originate from the anarchist and radical left. It was also refreshing to read something about networked resistance that didn’t slyly imply that those who engage in resistance against capitalism are, if not actually terrorists, inadvertently helping them. I have a lot of familiarity with the movement, having participated in regional protests and actions since 2002.
I appreciated that Holmes knew what of he wrote. This sounds obvious, but much of what is written about the global protest movement is partly or wholly inaccurate. Still after a decade and a half after the first WTO protests, for example, writers still refer to the Black Bloc as an organized group rather than the temporal tactic it is. Perhaps this is less of a surprise when we learn later in the article that the author himself was excitedly involved in the 1999 London J18 protest/street party.
Holmes is right that the systemic crisis allowed state actors to ramp up an overtly heavy-handed counter-resistance to the anti-globalization movement. If protesters hit on networked resistance, including decentralized leadership, flexible planning, and media opportunism, as a strategy to resist the carnival of capital marching inexorably forward, the agents of capital, while a little slow on the draw, were not unable to follow. Soon economic and leadership summits were turned into police states, and those who questioned the right of empire were branded as sympathetic to terrorists. The same-old tactics of networked resistance, summit hopping, we called it, was now a dead end.
Looking beyond the demise of the global protest movement, the people who seemed to learn the most lasting lessons were the agents of capital and their hired guns, that is: a heavy-handed focus on security is a more effective tool at controlling resistance in systemic crisis than a liberal (small L liberal) agenda. So that now, summit protesters, race rioters, radical queer activists, feminists who challenge the patriarchy, anarchists, animal rights protesters, all who interferes with the flow of capital, are branded terrorists.
In their 2007 piece “Nodes,” Galloway and Thacker argue that in a decentralized and networked society, dominant forces have reorganized themselves to adjust to the difficulty of top-down control. They argue an authoritarian epistemological shift from hierarchy to networks. They also argue that protocols control the exchanges made over networks.
This matches our sneaking intuition (and something that Marshall McLuhan warned us about) that those who create and control the networks — no matter how benign and benevolent those agents seem — control the way that we use those networks. That is to say, we can’t wholly discern the motives of those who provide “free” services such as Facebook and Google, but we are dimly aware they are vying for our souls.
Protocols are a technology to direct flows of information over decentralized networks. As Galloway and Thacker see it, protocols are made of complex relationships that emerge through autonomous interconnected agents, emerging through debate and negotiation. They are robust and flexible, inclusive, and universally applicable. If protocols control the exchange through the network, the big questions for me are:
- Who gets to design the protocols?
- Who gets to know the entire network?
- What benefits derive from providing the protocols and the network?
Clearly, these are the people who win.
In the last ten years, we’ve seen a shift from centralized to decentralized control. Rather than the FBI’s powerful G-Man, we see decentralized Joint Terrorism Task Forces (JTTF) working with local law enforcement. We see surveillance moving online as with the National Security Agency’s global surveillance program which it reassuringly claims is only used to watch non-citizens and terrorist connections (without ever elaborating on who gets branded a terrorist in our current security-obsessed context).
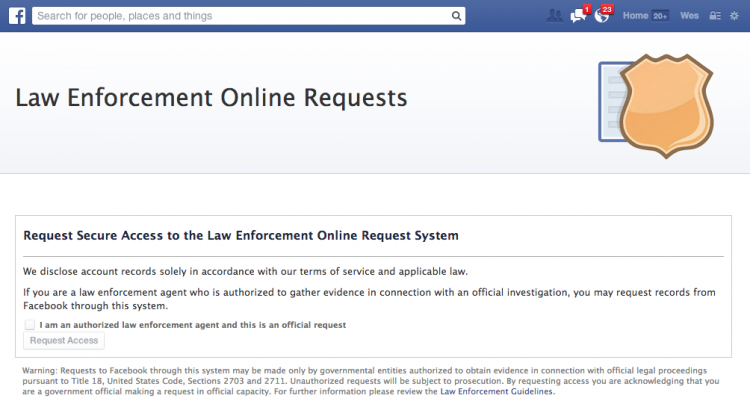
Increasingly, we see the new networked forces collaborating with the old centralized control. Facebook has an entire page devoted to helping law enforcement, helpfully filed under “safety.” In fact, the Law Enforcement Online Request System can be accessed with no more than an assurance that you are “a law enforcement agent who is authorized to gather evidence in connection with an official investigation.”
The confirmation email one gets after submitting this page says:
The following link allows authorized law enforcement officials to securely access our Law Enforcement Online Request System. The link expires in one hour. You do not need a login or password. If you do not use this link within an hour, you must return to facebook.com/records to request a new secure link.
To access our Law Enforcement Online Request system click https://www.facebook.com/records/x/login/auth/?token=xxx
Thank you,
Law Enforcement Response Team
This is not an academic question. Do police routinely read your Facebook profile as part of their investigations? Yes, of course they do. Facebook, Twitter, Tumblr, and online networks are a dream for police investigators. Where they used to have to go out and interview people, check records, walk the street, now they merely have to go online. Investigation from the convenience of their offices.
A few years ago, I took part in a demonstration and was arrested on seriously questionable legal grounds. I later requested a copy of the police report and was surprised to find that the police had gone beyond just the basic facts of my arrest. They has tracked down my personal Myspace profile in which I had some pretty cheeky anti-authoritarian hyperbole. It was taken wildly out of context and quoted in the report. “Subject says in his myspace profile that he is ‘looking for someone to turn over and burn police cars with,'” a dumb comment that had been part of my online profile for many years. There was a printout of my entire myspace, facebook, and website. They passed all of this information on to my employer with a suggestion that they look into it.
While I wasn’t arrested burning police cars, nor was there any suspicion along those lines (I was caught redhanded playing music), my employer took it seriously enough, especially coupled with a heads-up from the local police. The implication and insinuation that someone is involved in something nefarious can easily be made. If you are engaged in resistance of any sort — even artistic resistance — don’t think for a minute that just because you are non-violent (and even law-abiding) doesn’t mean you can’t be charged with something.
Imagine what might be said about your online profiles. For instance, it is not hard to imagine this showing up in the usual exaggerated claims of an indictment: “Subject follows on Twitter ‘Action for Animals.’ This is a group with connections to the Animal Liberation Front, whose members have been convicted of arson and long watched by the FBI as a serious potential domestic terrorist threat.” Bullshit and circumstantial connections notwithstanding, the implication is there for a prosecutor to use and with which the media can make hay.
While I don’t imagine that local law enforcement has the time or resources to randomly surf online sites in order to make connections, they do investigate people who’ve come to their attention. It is certainly not beyond the means of the feds or the many JTTFs to map out networks of connections and involvement. Online profiles and blogs have definitely been used against people in criminal cases.
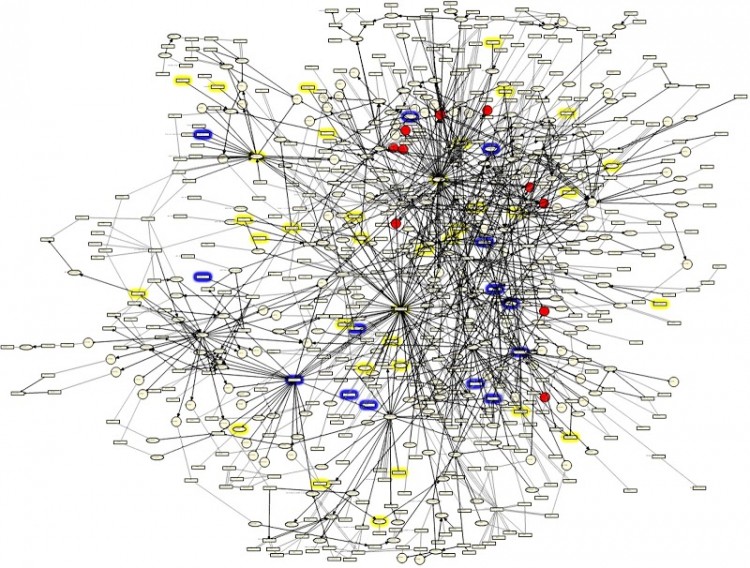
To be clear, it isn’t the usual individual privacy concerns that I am highlighting here. I am not wholly concerned with the fact that Facebook and therefore the feds know that I had sushi last night or even that I shared an article about police abuse at DUI Checkpoints from CopBlock. The interesting concern is about our aggregate network, the connections we share, not just one of us, not just me or you personally, but all of us. If you control — or better! provide — the network, you know who knows who and what they talk about.
This brings up one of the most empty assurances I’ve heard in the last decade. When it was first revealed that the US government engaged in warrantless surveillance of phone networks in the early 2000s, they assured us that there was nothing to worry about because without a warrant, they only viewed the “envelope information.” This is also called a pen register tap or a tap-and-trace. That is, the government didn’t listen in on your calls or read your texts, they only tracked who and when you called or texted. Later, it was revealed that the NSA records envelope information for domestic email as well. But relief that they are not listening to our calls misses the point of what they do get: the entire network topology, the configuration of the global communication network, the Who Knows Who of the Information Age.
All of this brings up some questions for me. How do we bring forward the benefits (or risks) of knowing the topology of a network? How do we feel that some institutions know everything about all of us, including who we know? How do they use that information? What does resistance to control look like in a networked society in which the tools and protocols we use are out of our control?
By nature, I respond to serious threats with grim humor and creativity. As an artists, I had an idea to create software that would playfully (but seriously) extract your social media footprint from public network sources, Facebook, Google+, Twitter, and so on. It could create your personal social network topology, extracting trends and keywords, noting possible threats and concerns and implications. I think it would be both technically challenging and conceptually easy.
In activist hands, such a tool could prove useful. Imagine being able to quickly turn up thee network of corruption surrounding those in office. But like all tools, it cuts both ways.
Though I conceived of this some years ago, I never pursued it because it depressed me. Creating such a beast is no doubt a dangerous game to play, like experimenting with a deadly and virulent virus. Precisely the kind of thing that I could imagine accidentally moving from an art context (“Whoa, looks what terrible thing is possible!”) to a law enforcement context (“The People of the United States vs. You”). A self-destruct mechanism for dangerous tools is always critical.




Not having a social media account for reasons of avoiding this sort of judicial persecution is also turning into a reason for suspicion.
It’s soul boggling and stupid… I want to run away.
have you seen this? https://immersion.media.mit.edu/ i too, once thought of writing a similar program. i’m not convinced it’s dangerous only because i’m sure this work has been happening behind closed doors for years. but it is illuminating when hackers/artists show what’s possible.
it’s scary how well it works.
digging the fun-a-day blog!
Nick, immersion was fun to play with. It reminded me a bit of FOMOphobia my fall piece in that it made the normally private world of email visible.